Spectacular Tips About How To Detect Computer Intrusion
October 8, 2017 linas kiguolis 0.
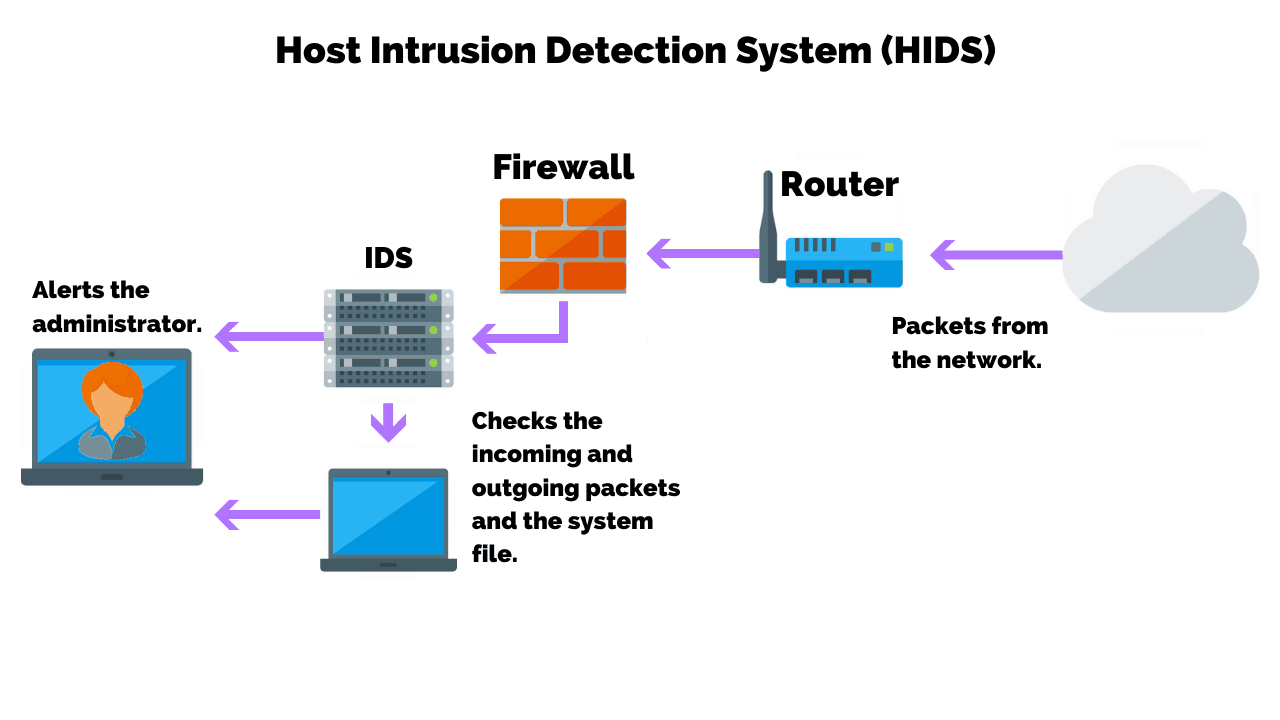
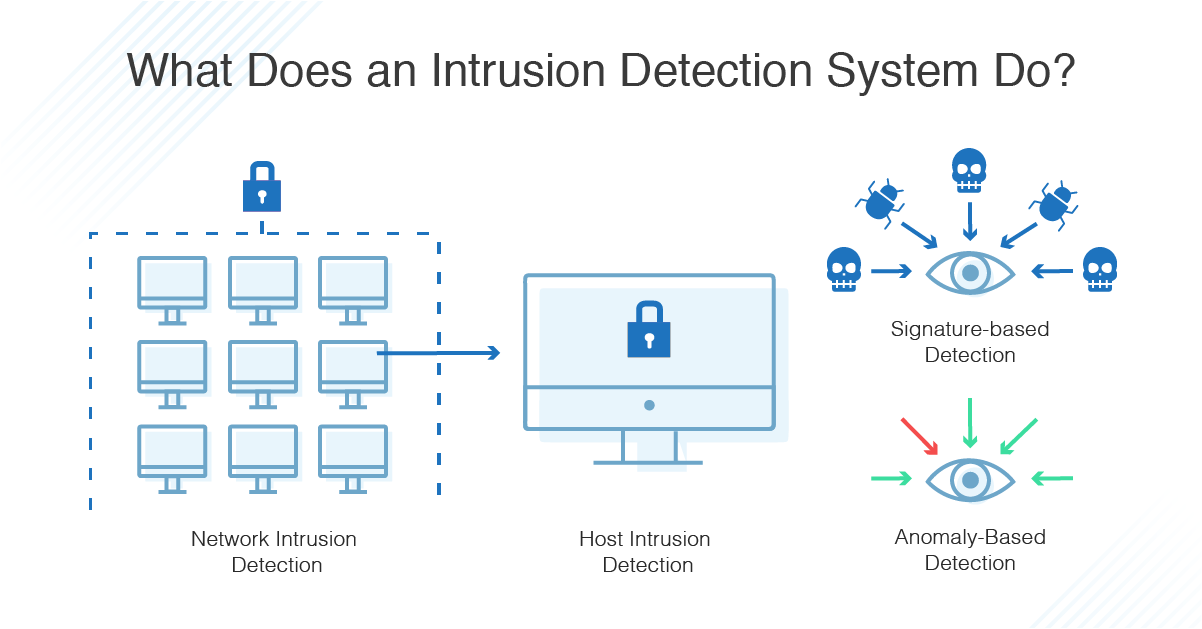
How to detect computer intrusion. Novel intrusions can be discovered by anomaly detection methods. Learning to detect computer intrusions with (extremely) few false alarms jude shavlik mark shavlik Host intrusion detection systems (hids) run on independent hosts or devices on the network.
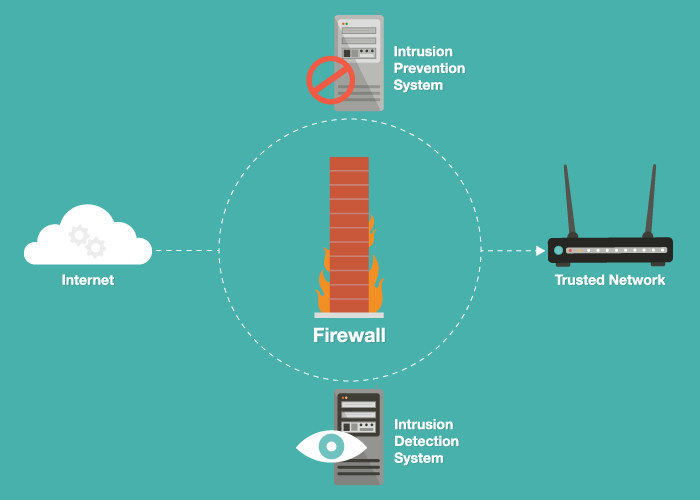
Table of contents [ hide] 1 tools to detect unauthorised access to your computer. An intrusion detection system (ids) can be a helpful addition to your information security plan. Standard group plc hq office, the standard group center,mombasa road.
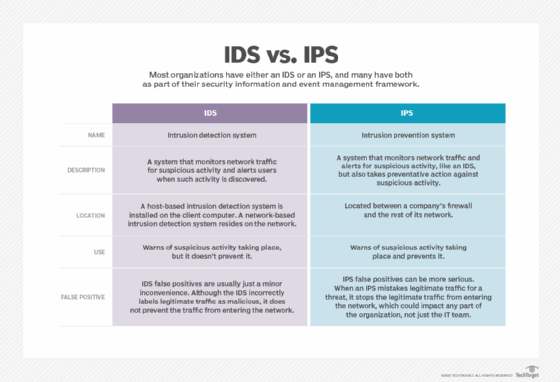
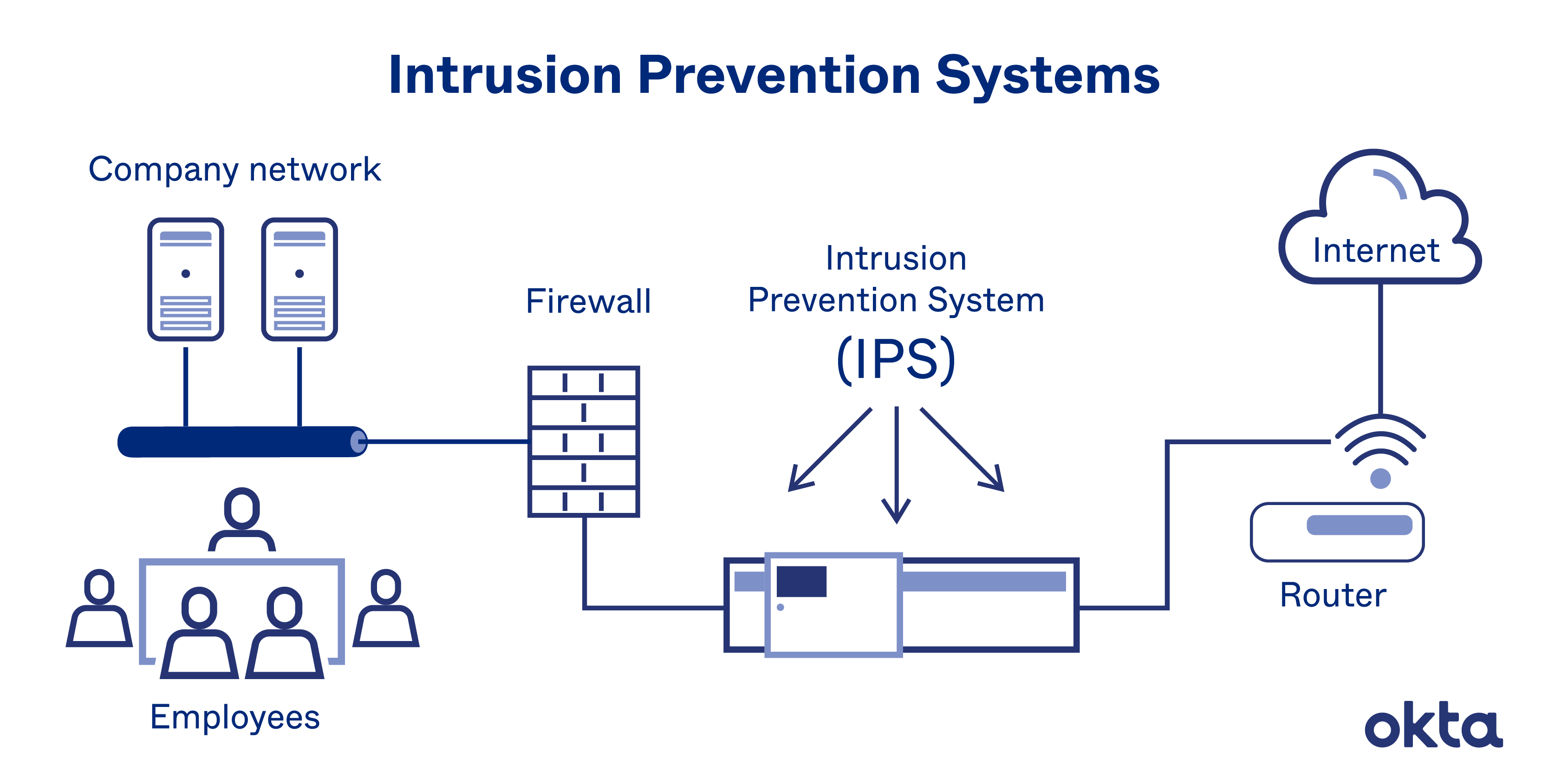
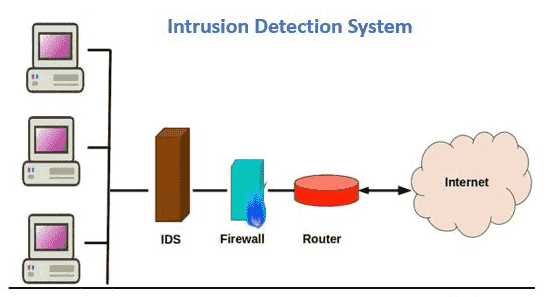
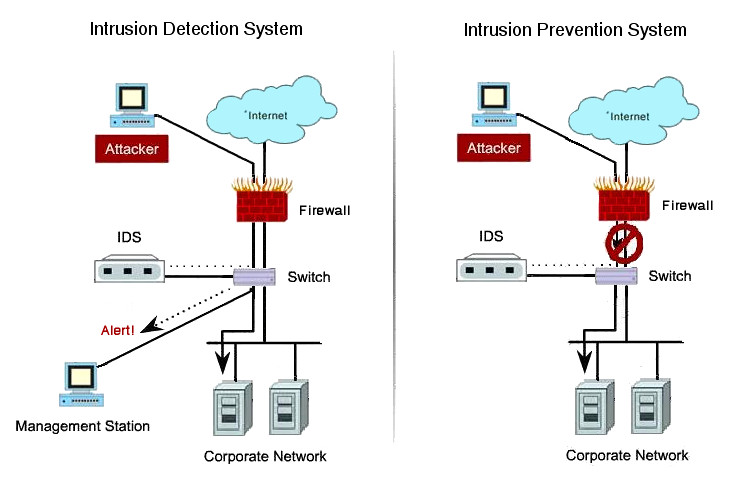
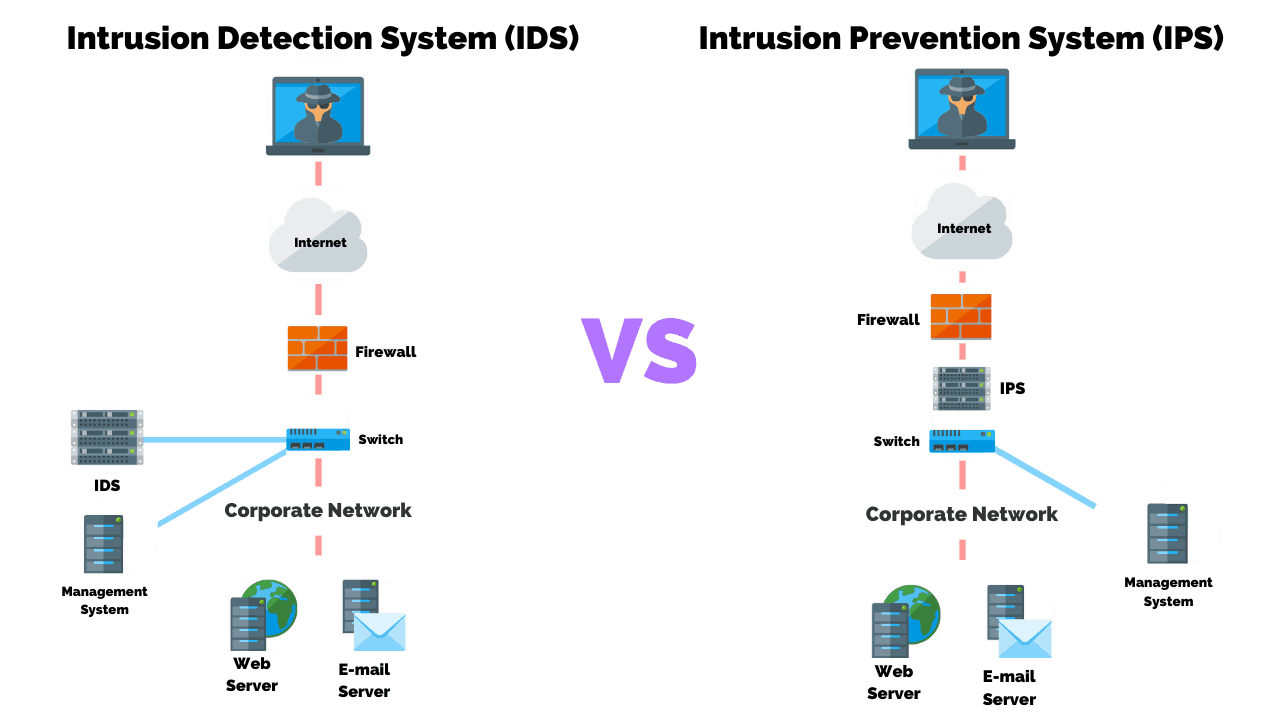
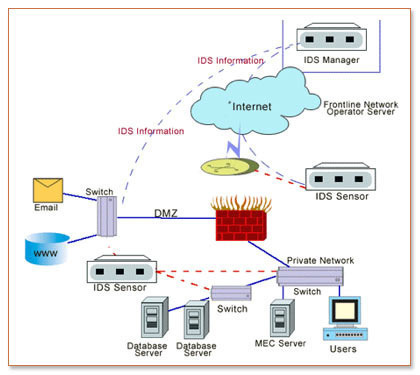
Intrusion detection system (ids) an intrusion detection system (ids) is a monitoring system that detects suspicious activities and generates alerts when they are detected. A hids monitors the incoming and outgoing packets from the device only and. This hacking tutorial presents a crash course on the subject of.
How to detect computer intrusion. Intrusion detection via the windows event log detecting failed logons. An ids will also generate alerts, log relevant information, and attempt to block or.
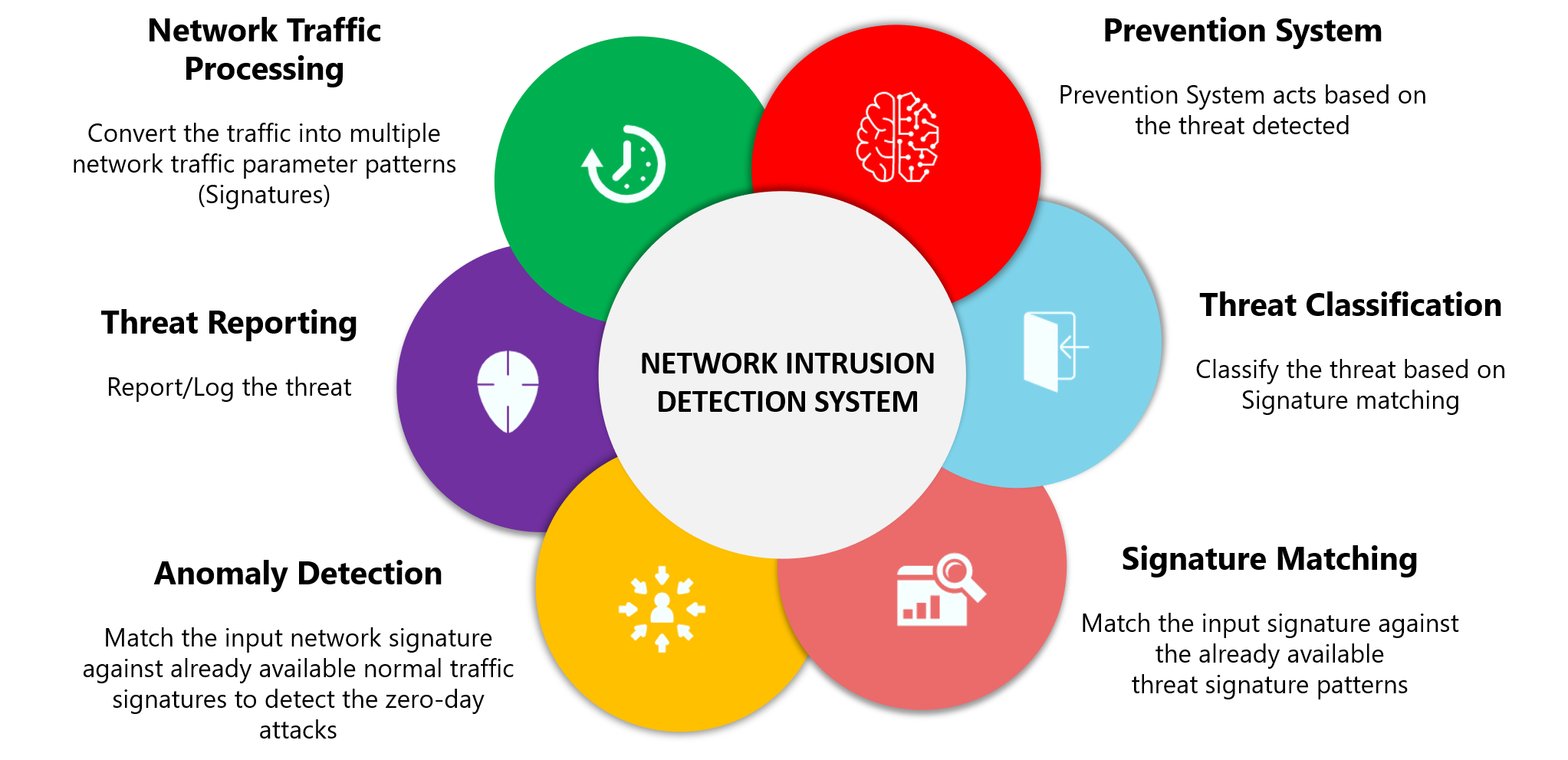
Anomaly detection constructs models of normal network behavior (known as profiles), which can detect. They detect suspicious activity by inspecting network packets and identifying oses of services. These tools regularly monitor network traffic (network intrusion detection.
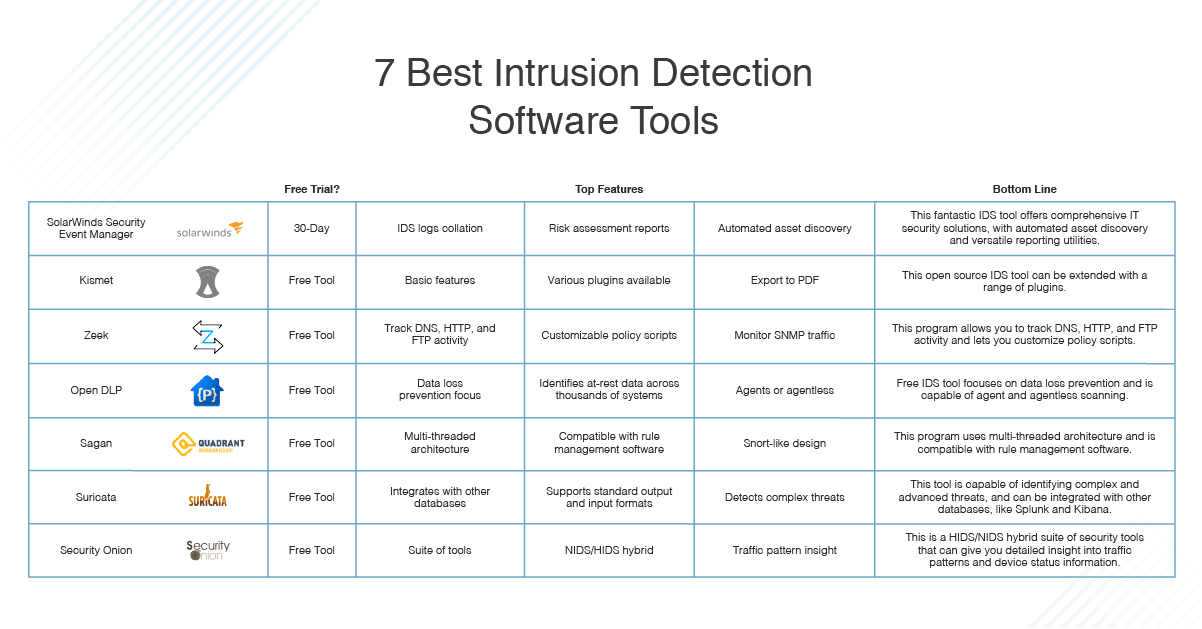
5 best intrusion detection software. Detecting intrusion organization of #operations. How to detect computer intrusion i survived stage 4 liver cancer, what are the markers for lung cancer, how do you get test for covid antibodies.